A few months ago, while analyzing network traffic patterns to optimize DNS routing for a client's server, I noticed an alarming trend in user behavior. During a brief testing phase for a new community platform, hundreds of users were happily handing over their primary, permanent mobile phone numbers just to view a single hidden forum thread. They were permanently linking their core digital identity to a fleeting experiment. From an infrastructure-engineering perspective, I focus heavily on network security, and observing this automatic surrender of private data made it clear that our approach to account verification is fundamentally flawed.
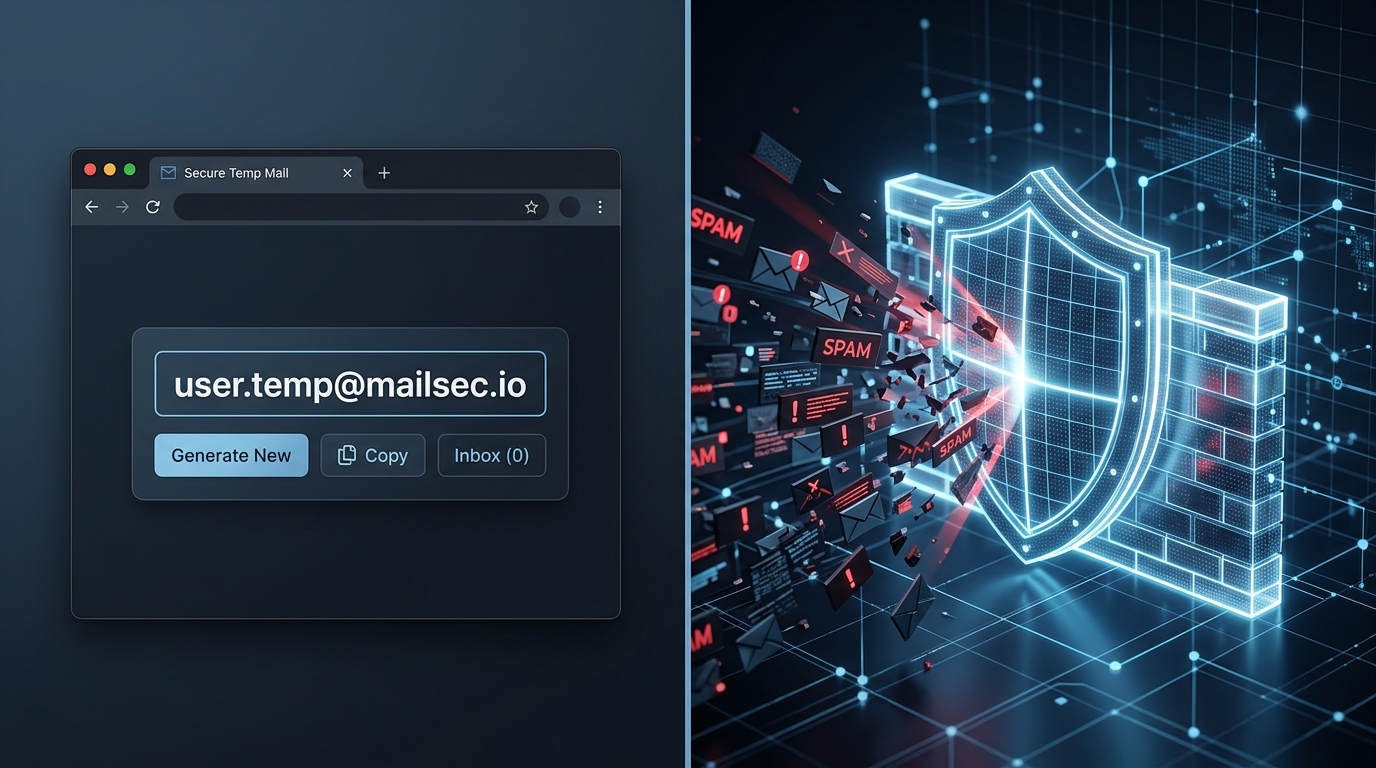
Receive SMS&Temp Mail: CodeApp is a service-based verification tool providing shared temporary SMS numbers and disposable email addresses for users who need to receive sign-up codes without exposing their personal contact information. Instead of functioning as a traditional communication app, it is engineered specifically to bypass verification gates for platforms like WhatsApp or Instagram, allowing users to verify accounts and discard the temporary connection immediately.
As app usage continues to scale, deciding how you verify your identity requires a strategic approach. We need to compare traditional secondary numbers against purpose-built verification workflows to understand what actually protects your privacy.
The application economy requires a dynamic approach to privacy
We are registering for more digital services than ever before, and the data backs this up. According to the "Mobile App Trends 2026" report by Adjust, global application installs are projected to rise by 10% in 2025, with user sessions increasing by 7%. Meanwhile, consumer spending in the mobile ecosystem has reached a significant $167 billion. The report highlights that mobile growth in 2026 will be heavily driven by AI-supported analytics and multi-platform measurement architectures.
What does this mean for you? It means tracking is becoming incredibly sophisticated. The Adjust data also shows that App Tracking Transparency (ATT) opt-in rates among iOS users climbed from 35% to 38%. People are becoming slightly more willing to be tracked by developers they trust, but this trust is often exploited. Every time you download a new app to test a feature, you are hit with a verification wall. If you use your real phone number, that data is instantly fed into these advanced measurement architectures.

Persistent VoIP numbers fail modern SMS verification filters
When users realize they need to protect their primary number, their first instinct is usually to download a generic calling application. This is where the comparison between traditional VoIP (Voice over Internet Protocol) and dedicated verification tools becomes critical.
The Traditional VoIP Approach: Tools like Google Voice, TextNow, and Talkatone were built for persistent communication. They provide you with a dedicated 2nd phone number designed for making actual phone calls and sending personal text messages. If you search for a "text free" solution, you will usually find applications that function like a traditional burner phone. The user expects to hold onto this number for months or years to talk to clients or friends.
The Shared Verification Approach: In contrast, Receive SMS&Temp Mail: CodeApp operates on a shared, temporary pool model. It does not provide a persistent personal line for calling your family. Instead, it offers rotating numbers explicitly filtered for service verification.
The core issue with using standard virtual number providers for account creation is filter rejection. Modern social media platforms maintain massive databases of known VoIP blocks. When you attempt to register using a TextPlus or standard second number, the platform's security algorithm often flags it as a high-risk virtual line. By focusing strictly on shared service-based routing, tools like CodeApp can rotate access points, ensuring a higher success rate when you merely need to receive a six-digit code and move on.
Creating a new email address should not be a permanent commitment
Just as people mistakenly use heavy communication apps for simple SMS checks, they also overcomplicate email verification. Suppose you are browsing an automotive community to research the reliability of a Dacia Logan sedan or comparing the battery degradation curves of a Skywell SUV. The forum requires you to create an account to view the technical attachments.
The Standard Email Method: You decide to open a new email address specifically for junk registrations. You go to a major provider, fill out your name, and provide a recovery email. Even if you use a custom domain email address, you are still actively managing an inbox that will inevitably fill up with spam. You are exchanging long-term inbox maintenance for five minutes of forum access.
The Temp Mail Method: A temporary mail address generates instantly. There is no password, no recovery linking, and no personal data required. You copy the mail string, paste it into the forum registration, click the activation link that appears in your temporary inbox, and close the session. The inbox ceases to exist shortly after.
Users increasingly demand isolation without the overhead of maintaining persistent credentials. The market is moving away from permanent secondary accounts toward ephemeral verification workflows that prioritize speed and privacy.

Evaluation criteria dictate the right verification method
Choosing the correct tool depends entirely on your target outcome. In practice auditing security protocols, applying the wrong verification layer either locks you out of your accounts or unnecessarily exposes your data. Here is a practical framework for selecting your method:
- For highly sensitive, long-term security (Banking, Primary Email): You must use a hardware key or a dedicated authenticator app. An authentication app generates local, time-based codes that cannot be intercepted via cellular networks. Never use a temporary number for your bank account.
- For long-term client communication (Freelancing, Small Business): A persistent 2nd phone number is the right choice. Applications that act as a virtual secondary phone allow you to maintain an ongoing dialogue with customers without revealing your personal cell.
- For short-term account creation and testing (Social Media, Web Forums, App Trials): This is where Receive SMS&Temp Mail: CodeApp excels. If your goal is strictly to bypass an initial sign-up gate without permanent tracking, a temporary SMS or temp mail service is the most efficient choice.
CodeApp is built specifically for users—such as quality assurance testers, freelancers researching competitors, and privacy-focused individuals—who need fast access over permanent ownership. It is not designed for users looking to replace their daily texting habits.
If you are exploring the broader ecosystem of digital privacy, our parent company Verity also develops tools focused on secure infrastructure, ensuring that your network connections remain as isolated as your verification workflows.
Speed and isolation matter more than bloated features
The next time you are prompted to enter a phone number to read an article or test a software tool, pause and evaluate the request. Are you establishing a long-term relationship with this platform, or are you just passing through?
Generic communication apps are weighed down by features you don't need for simple verification. They require persistent profiles, contact syncing, and ongoing background processes. By comparing these heavy communication clients against lightweight, service-based verification endpoints, the most secure path becomes obvious. Prioritize isolation. Use temporary access for temporary tasks, and keep your core digital identity strictly offline until it is genuinely required.